After our article on BYOD security questions raised by personal tablets and mobile phones in the workplace, what changes are taking place concerning the security of company applications and communications on personal mobile phones?
More and more, companies are letting employees receive their work e-mails on personal tablets and smartphones. However, some are still wary about providing access to professional applications and documents from personal devices, especially because of security issues.
In this article, I’ll talk about containers and wrappers, which are two ways to separate personal and professional use on a single device (smartphone or tablet). Both these methods are increasingly common on the market.
the container: its principles and derivatives
The idea behind containers is pretty simple: the point is to store professional applications and data in a zone that is completely separate from personal use. The advantage is that no data will exit the professional zone and enter the personal zone.
But things start to get a bit tricky when you try to set up this solution. There are two different types:
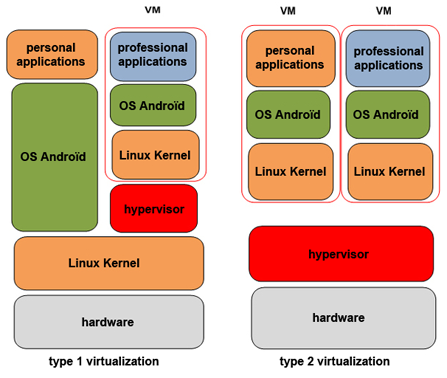
- type 1 virtualization: this installs a hypervisor to run a virtual machine complete with a kernel, an operating system (OS), and the professional applications located on top of the hardware layer and original kernel
- type 2 virtualization: this installs a hypervisor on top of the hardware layer to run two virtual machines, each containing a kernel, an OS and professional applications
advantages and disadvantages of containers
While the advantages are fairly obvious (high level of security, since data remains encrypted even if the device is lost or stolen), containers still present a few major disadvantages:
- complex installation (changes to be made on the phone and the terminal’s ROM)
- currently only available on Android
- uses a lot of energy and processing power, thus reducing battery life and significantly impacting the end user’s experience
I'll show you in a second blog post another way to split professional and personal zones.
Philippe
photo credit: © auremar - Fotolia.com
This blog post was originally published in French here.

After previously working as a training manager, on-site IT officer, pre-sale technical officer, and customer service manager, I joined the Orange Business security team as a product manager. I’m very committed to the user experience and easy administration of the solutions we create. My watchwords: knowledge sharing, logic, pragmatism and simplicity.